Unlocking the Power of Nmap: A Comprehensive Guide
Written on
Chapter 1: Introduction to Nmap
Nmap, short for "Network Mapper," stands as a free and open-source tool designed for network exploration and security assessments. It employs raw IP packets to uncover details about hosts, services, operating systems, and the types of packet filters or firewalls present on a network, alongside a multitude of other characteristics. This versatile tool is compatible with all major operating systems and can be utilized through a classic command-line interface or its graphical counterpart, Zenmap.
Nmap serves as a powerful application for network scanning, enabling users to identify devices connected to a network and gather insights about their active services and operating systems. For many users, including myself, Nmap is the first step in assessing the security landscape of a target.
Section 1.1: Key Features of Nmap
Robust Capabilities
Nmap excels in delivering insights on active IPs within a network, providing a comprehensive overview of network characteristics, listing available hosts and open ports, as well as identifying the operating systems of connected devices.
Versatile Installation
Nmap is easily installed on various operating systems, including Linux, Mac, and Windows. This tool can be integrated with other applications like the Metasploit framework to enhance its functionality.
User-Friendly Operations
Most common Nmap functions can be executed using straightforward commands, and the program also offers numerous simple features to automate routine tasks.
Accessible Command-Line Interface
Users can access Nmap by simply typing nmap in the terminal followed by specific arguments or switches that dictate its actions.
Helpful Documentation
Nmap includes a built-in help feature that outlines all available flags and options. Familiarizing yourself with this help function is essential due to the extensive library of command-line arguments it supports.
The first video provides an overview of Nmap and Angry IP, two essential open-source tools for IP scanning that every user should be aware of.
Subsection 1.1.1: Scanning Techniques
Port Scanning
TCP Connect Scan: Typically noisy, this scan can be easily detected as it logs the sender's IP address and may trigger Intrusion Detection Systems.
Command: nmap -sT <IP>
UDP Scan
This scan checks for open UDP ports on the target machine. It's generally slower and may lead to false positives.
Command: nmap -sU <IP>
SYN Scan
A stealthy technique that sends specially crafted SYN packets to initiate a TCP connection without completing it.
Command: nmap -sS <IP>
ACK Scan
This method determines whether a specific port is filtered.
Command: nmap -sA <IP>
Version Detection
Identify the service version running on a specific port.
Command: nmap -sV <IP>
Operating System Identification
Determine the target's operating system.
Command: nmap -O <IP>
Aggressive Scanning
This option enables OS detection, version identification, and script scanning. However, it generates more probes, increasing the likelihood of detection.
Command: nmap -A <IP>
Port Specification
By default, Nmap scans common ports unless specified otherwise. You can perform scans for specific ports or ranges.
Commands:
nmap -p <port> <IP>
nmap -p <port-range> <IP>
nmap -p- <IP> (for all ports)
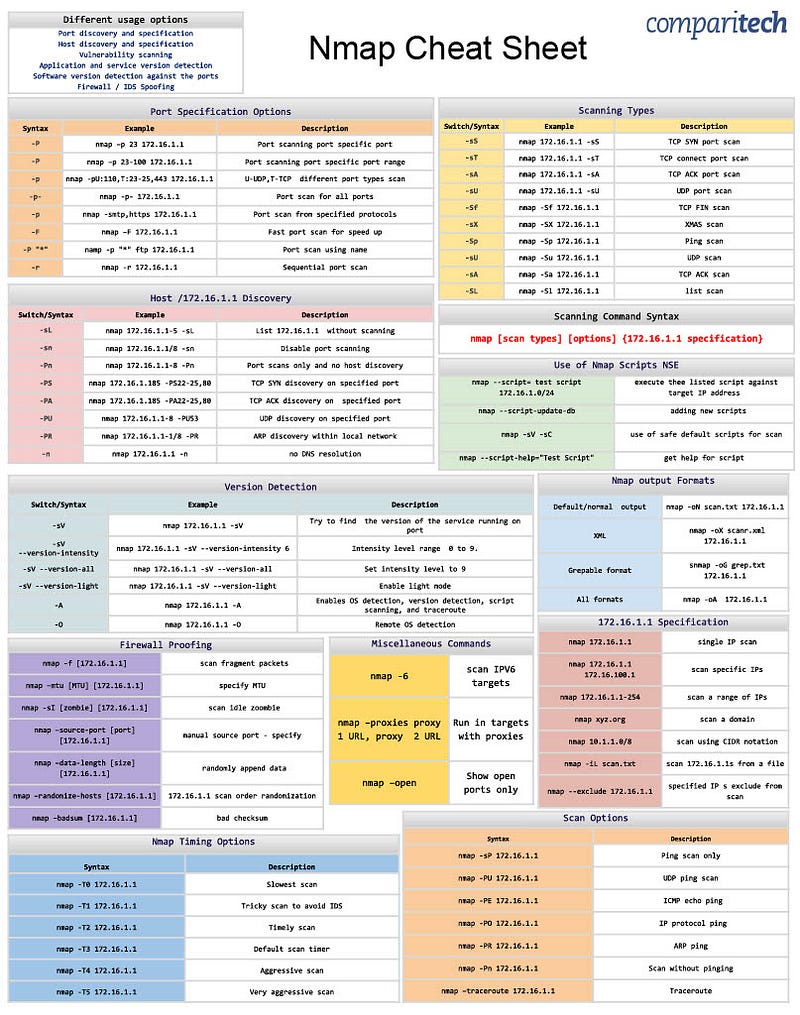
Chapter 2: Nmap Cheat Sheet
Nmap is often referred to as the "Swiss Army Knife" of networking due to its vast array of commands. It enables users to efficiently scan and gather data on networks, hosts, ports, firewalls, and operating systems.
The second video is a complete tutorial on Nmap, guiding beginners through advanced concepts in cybersecurity and network analysis.